FHICT joins Challenge The Cyber 2021
 Saturday, May 29, 4 teams of FHICT participated in the annual Challenge The Cyber challenge. Challenge The Cyber is an initiative of the National Cyber Security Centre and dcypher. During this challenge, pupils and students from different institutions have to compete against each other in teams of maximum 5 students to solve CTF's with the aim to get the most points at the end of the day. These points are obtained by finding flags that are encrypted, hidden or hard to find. These flags are captured by hacking and decoding files.
Saturday, May 29, 4 teams of FHICT participated in the annual Challenge The Cyber challenge. Challenge The Cyber is an initiative of the National Cyber Security Centre and dcypher. During this challenge, pupils and students from different institutions have to compete against each other in teams of maximum 5 students to solve CTF's with the aim to get the most points at the end of the day. These points are obtained by finding flags that are encrypted, hidden or hard to find. These flags are captured by hacking and decoding files.
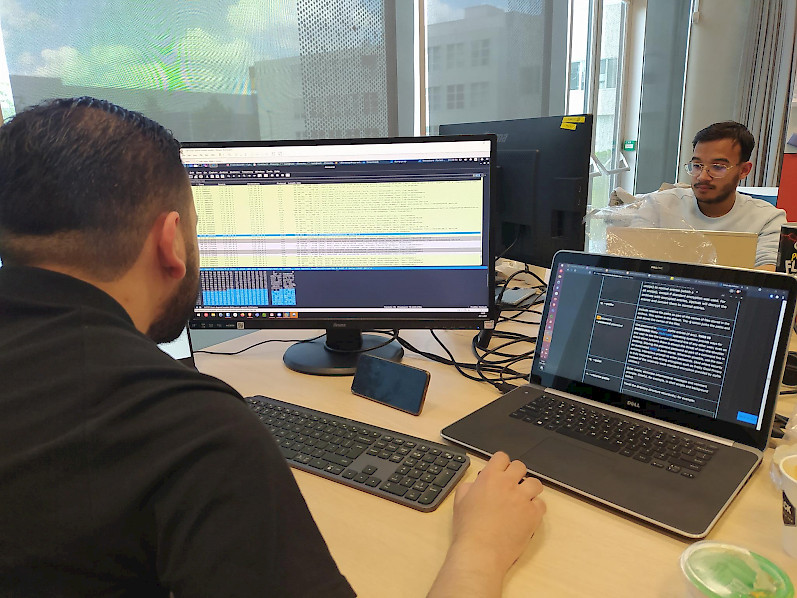
This event was held in the form of a live stream and can be viewed at. During this stream, the progress of the various teams was monitored and various topics relating to Cyber Security were discussed. The 4 teams that participated on behalf of Fontys are: Purple Brigade, APT013, Dutch Cyber ICT & LASTBUTNOTLEAST. These teams were present in Tilburg during this event to compete against each other.
In total, 36 teams participated in the Challenge The Cyber event ranging from vwo school students to various universities between the ages of 13 and 25. In the first hour of the event, the Purple Brigade team had a good start and was even in 2nd place. (See image 2). Towards the end of this event, the team APT013 finished in 10th place for the senior category with a score of 650 points. The Purple Brigade team finished in 12th place with 525 points.
The CTFs during this event can be divided into several categories. These categories consisted of:
- Cryptography: The goal is usually to crack or clone cryptographic objects or algorithms to reach the flag.
- Steganography: Usually a media file is given without further instructions. Participants must be able to unravel a message encoded in the media.
- Web: This type of challenge focuses on finding and exploiting vulnerabilities in web applications.
- Binary exploitation: Binary exploitation involves exploiting a bug or vulnerability to unintentionally perform other tasks in an application.
- Reverse engineering: Converting machine code, byte code to a human-readable format with the aim of understanding a particular program and identifying deeper problems.
- Networking: The analysis of network data to determine what is happening on a computer network. Often a pcap analysis.
- IOT, OS, PWN and miscellaneous.
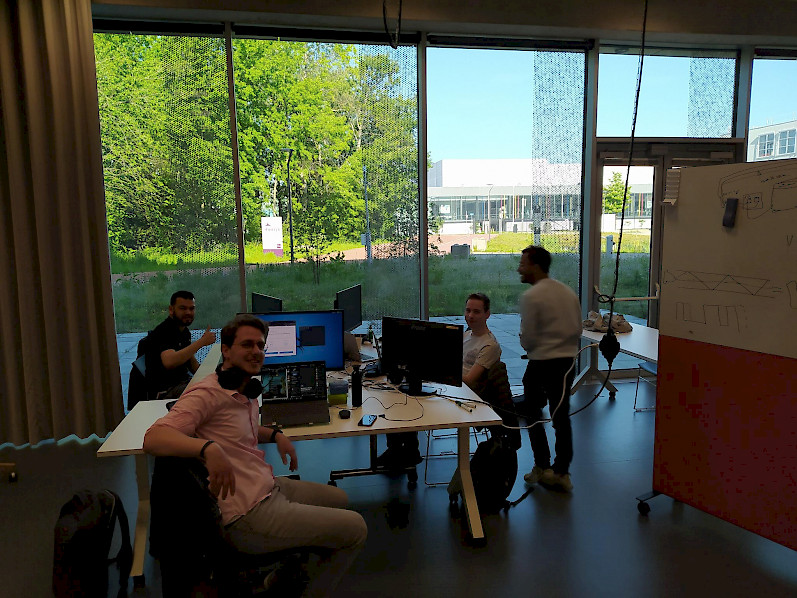
The level of difficulty was actually higher than expected. For many of the students, it was the first time they had participated in this event. The categories ended up being different than anticipated. The challenges were certainly tough, but have motivated the groups to perform better next year. It is definitely a must to participate if you are interested in Cyber. Figure 3 shows one of the teams: "Purple Brigade".
Text by Mario van Hoppe (cybersecurity student), Ron Mélotte (cybersecurity lecturer)